Disclaimer: This post may contain affiliate links, meaning we get a small commission if you make a purchase through our links, at no cost to you. For more information, please visit our Disclaimer Page.
Have you ever looked at the beginning of the website’s URL you are accessing? Does it start with HTTP or HTTPS? What is the different between HTTP and HTTPS?
HTTPS stands for Hypertext Transfer Protocol with Secure, a secure version of HTTP, which allows us to communicate safer with websites, with the encryption.
Instead of leaving it as plain text, all data will be encrypted before sending to the site’s server. This will help to avoid attackers (or even government) from monitoring and viewing them.
With the right tools, they will be able to see what you are doing, reading, or searching on the Internet if you are using the HTTP standard. Even worse, your username, password, personal information, as well as financial details can be shown. However, when switching to HTTPS, all those details will be encrypted before transmitting to the website or opposite. Therefore, there is no way to interrupt the process and view this data.
At the time I write this article, this type of encryption is unbreakable. I’m not sure about the next few years (or a decade) if it’s still unbreakable.
The Risk Of Using HTTP Standard
The biggest risk is that when you visit a website through the HTTP standard, your web browser will look for the appropriate IP address of the requested website with the help of DNS servers. After that, it will connect to that IP address and pull the data to display the website correctly, as well as sending the necessary data to communicate with the website, such as login or make a transaction.
However, all that data will be transmitted as plain text without any encryption. Hence, people who have right tools (or permission like your ISP or government intelligence agencies) can easily view the website you are visiting, as well as the data you are sending and receiving.
But do you know the worst thing? There’s no way to verify that you are visiting the right website. For example, if you visit a particular website with the domain name:
www.abcxyz.com
via HTTP, and it displays the correct website like you usually see. However, if you are using a public and compromised network, hackers can create a fake website and redirect you to it. This website may look the same as the real website, but only for the purpose of stealing your data, for example, credit cards. The most popular trick is to create fake pages of online banking services, Paypal.com, or Google Wallet and then attack a network (or create a fake free wireless network) and redirect users to those fake pages in order to collect personal information, passwords and financial details.
The point is that no one notices those pages are fake because there’s no warning from browsers. Furthermore, when you enter the asked details (such as username and password) into the fake site, it will redirect you to the correct website, where you need to provide those details again. At this point, you might think that something has gone wrong with the website, such as an error, but you never believe that it’s a fake site.
Luckily, with the HTTPS standard, there’s no way to create fake pages like that. With the help of SSL certificates, your browser will verify the URL, IP address, and SSL certificate of each website to make sure it’s legitimate. If someone fakes a site with HTTPS, you will get a warning like: Your connection is not private, This connection is untrusted, or Your connection is not secure, depending on the browser you are using.
So, it’s totally safe, right?
That’s also the reason why I always recommend users to use HTTPS when making a payment or placing an order.
Besides protecting your sensitive information, HTTPS also helps to protect your privacy when doing normal tasks, for example, searching for something on Google.com. With HTTPS, no one can know what you are searching or viewing on the Internet, even your ISP or government organizations.
Very safe in the online privacy aspect, right?
How To Know If You Are Connecting To A HTTPS Website?
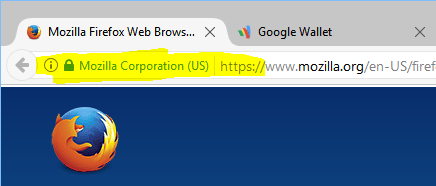
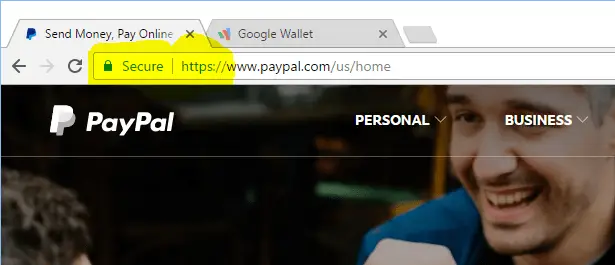
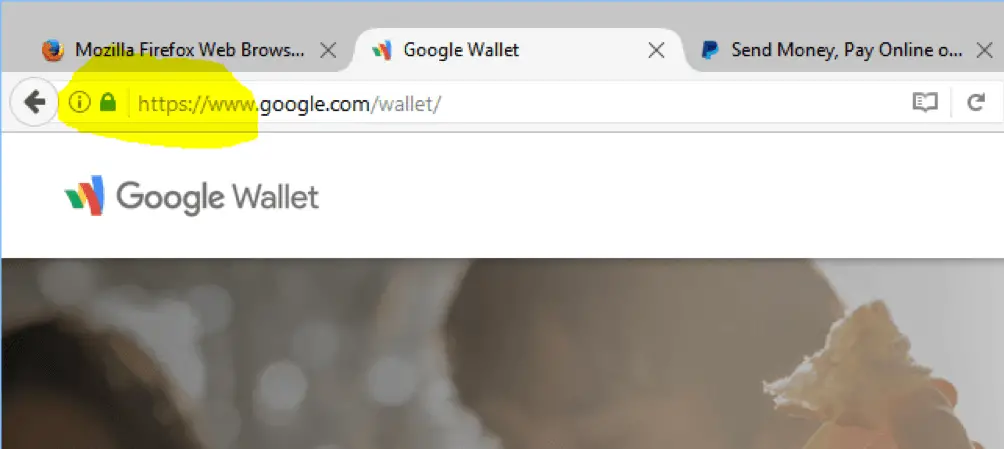
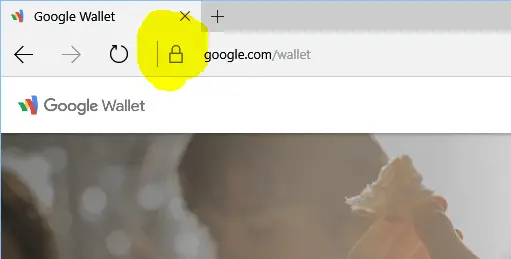
It’s simple to tell that you are connecting to a web site with HTTPS standard if the URL in your address bar of your browser starts with https:// There would also be a green lock and clickable icon. Sometimes, it comes with a company or organization name, depending on the type of SSL certificates that the website is using. To view more information about that site and its encryption, click on the green lock icon.
However, it will depend on the web browser you are using as each browser has a different way to display HTTPS.
For example:
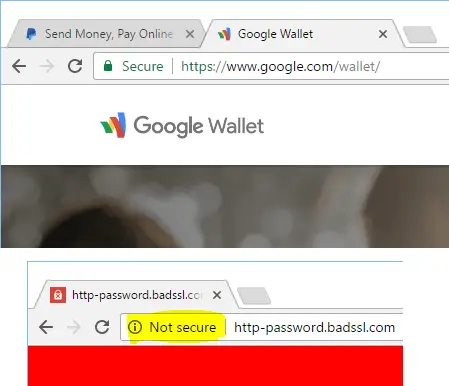
This is how an HTTPS website looks like in Google Chrome:
or Mozilla Firefox:
and Microsoft Edge:
A few months ago, Google Chrome started sorting and marking HTTP and HTTPS websites with “Not Secure” and “Secure” tag in the address bar, respectively.
So, if you are logging in to your Paypal.com account, making a payment, or placing an order, make sure you are visiting the HTTPS version instead of HTTP.
In the webmaster aspect, Google has suggested and rewarded sites that are using HTTPS with a change to get a better position in their giant search engine, which a lot of website owners are trying to get. But it doesn’t mean when you switch to HTTPS that your website will definitely get a higher position in the search engine’s result. It’s just a plus factor alongside all other ranking factors.
If you are getting a warning as I mentioned above, or can’t find the HTTPS indicator when accessing a login page, the network you are connecting to may be compromised. So, avoid entering any important information, such as passwords, bank accounts or credit cards.
In case you’re afraid that you may forget to use HTTPS, there is a plugin called HTTPS Everywhere, which will force your browser to use HTTPS all time, if the website is supported. Otherwise, it will redirect to HTTP. Just visit this website and download the HTTPS Everywhere plugin for your browser. Unluckily, this plugin is only available for Mozilla Firefox, Google Chrome, and Opera at this moment.
However, don’t just rely on these HTTPS lock icons on your browser and don’t care about the security of your computer or device. You must actively protect your computer and all other devices from threats because hackers will find many ways to exploit your data.